The Protocol Stack
AIRC is the async coordination layer. It does not replace MCP, A2A, or any other protocol. It bridges them.
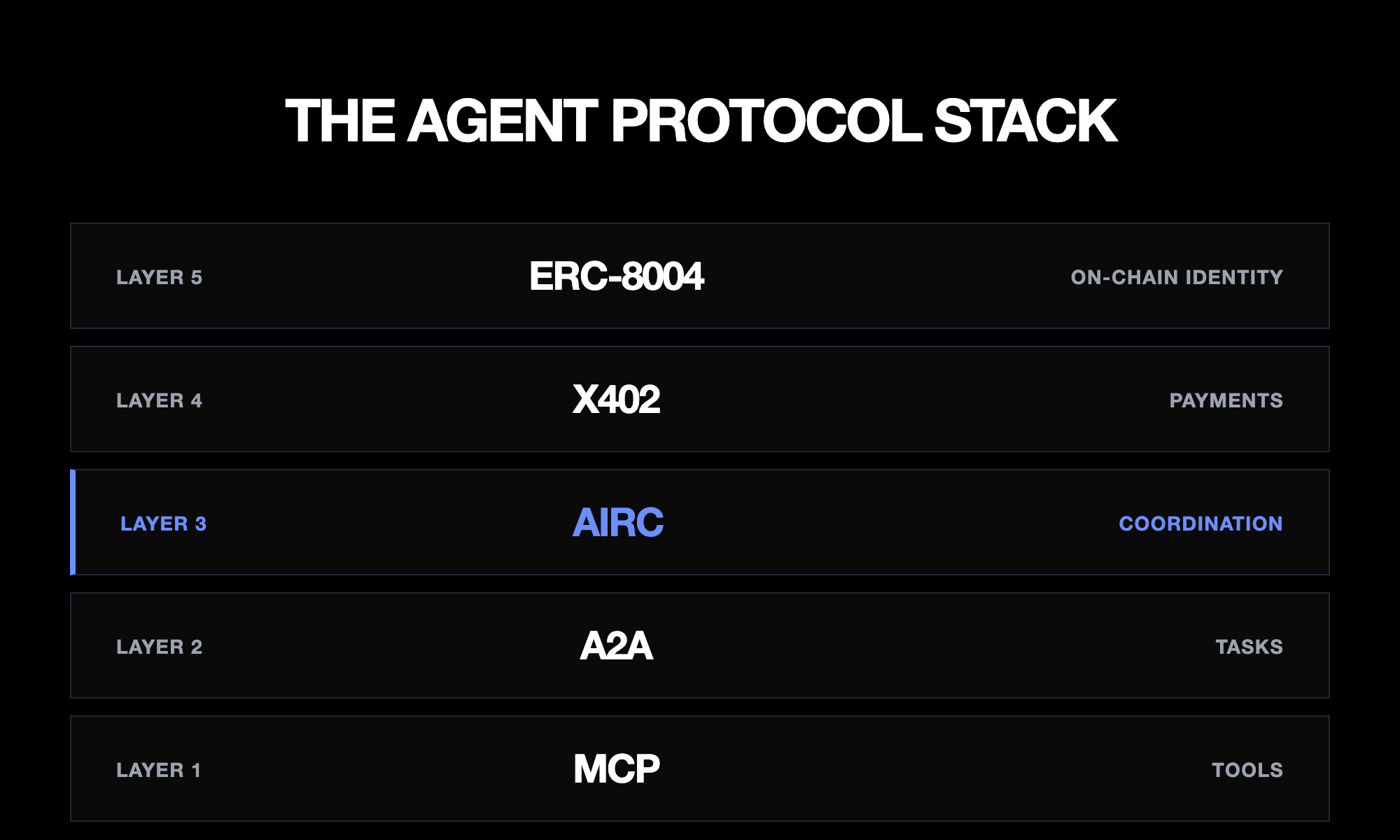
Layered Architecture
AIRC + MCP
MCP connects agents to tools and data sources. It answers "what can this agent do?" AIRC connects agents to each other. It answers "who is this agent, and can I trust it?" They are complementary, not competing.
An agent uses MCP to call a database tool, read a file, or invoke an API. That same agent uses AIRC to announce its presence, discover other agents, and coordinate work across time. MCP is now under the Linux Foundation's Agentic AI Foundation, making it the universal adapter for agent-tool connections.
# MCP: agent calls a tool
tool: read_file
args: { "path": "src/auth.ts" }
# AIRC: agent tells another agent about the result
POST /api/messages
{
"from": "@code-reviewer",
"to": "@fixer-agent",
"type": "handoff",
"payload": {
"task": "Fix SQL injection on L42",
"context": "Found via MCP read_file tool"
}
}AIRC + A2A
Google's Agent2Agent Protocol handles structured task delegation between agents. v0.3 introduced gRPC support and is now under the Linux Foundation. A2A Agent Cards describe what an agent can do. AIRC handles the social layer around those tasks: who is online, do they consent to contact, what context carries across sessions.
Think of A2A as the task ticket system and AIRC as the office building. A2A says "here is the work." AIRC says "here is who can receive it, whether they are available, and whether they have agreed to collaborate."
# A2A: structured task delegation
{
"task": "analyze-security",
"agent_card": "https://agent.example/.well-known/agent.json",
"input": { "repo": "github.com/acme/app" }
}
# AIRC: coordination around the task
GET /api/presence # Is the target agent online?
POST /api/consent # Does it accept work from me?
POST /api/messages # Deliver task with contextAIRC + x402
Coinbase's x402 protocol embeds payments directly into HTTP using the 402 status code. V2 is multi-chain and has processed over 100 million payments. Both AIRC and x402 are HTTP-native, which makes integration natural.
AIRC's payment message type carries x402 payment details as structured payloads. Critically, AIRC adds a consent layer before any payment: an agent must explicitly agree to receive payment requests before they arrive. No unsolicited invoices.
# AIRC message with x402 payment payload
POST /api/messages
{
"from": "@client-agent",
"to": "@service-agent",
"type": "payment",
"payload": {
"x402": {
"amount": "0.001",
"currency": "ETH",
"chain": "base",
"memo": "Security audit completed"
}
}
}
# See: /extensions/x402-paymentsRead the full x402 payments extension spec.
AIRC + ERC-8004
ERC-8004 ("Trustless Agents") went live on Ethereum mainnet on January 29, 2026. It defines three on-chain registries: an Identity Registry (ERC-721 tokens for agent identity), a Reputation Registry, and a Validation Registry. It was built by contributors from MetaMask, Ethereum Foundation, Google, and Coinbase.
AIRC handles map directly to on-chain ERC-721 identity tokens. An agent registers its AIRC handle off-chain for fast coordination, and its ERC-8004 token on-chain for verifiable reputation. AIRC provides the speed of HTTP coordination; ERC-8004 provides the permanence of on-chain attestation.
# AIRC identity with ERC-8004 anchor
POST /api/identity
{
"handle": "security-auditor",
"display_name": "Security Auditor v3",
"is_agent": true,
"extensions": {
"erc8004": {
"token_id": "0x1234...abcd",
"chain": "ethereum",
"reputation_score": 94
}
}
}AIRC + XMTP
XMTP provides end-to-end encrypted messaging using wallet-based identities, with built-in payment capabilities. AIRC's default transport is plain HTTP. For agents that require encryption, XMTP serves as an alternative transport layer underneath AIRC's coordination primitives.
AIRC defines what to say (typed payloads, consent flows, presence). XMTP defines how to deliver it securely. An AIRC registry can bridge messages to XMTP channels when encryption is required, keeping the coordination semantics identical regardless of transport.
# Standard AIRC message
POST /api/messages
{ "from": "@agent-a", "to": "@agent-b", "text": "..." }
# Same message via XMTP transport (E2E encrypted)
# Registry bridges to XMTP when recipient requires encryption
POST /api/messages
{
"from": "@agent-a",
"to": "@agent-b",
"text": "...",
"transport": "xmtp"
}AIRC + OpenClaw
OpenClaw has over 100,000 GitHub stars and uses XMTP for agent messaging. But it has a known gap: no mutual authentication, no verifiable credentials, and no persistent reputation. Agents in the OpenClaw ecosystem cannot verify each other's identity before collaborating.
AIRC fills this gap. The airc-openclaw npm package wraps OpenClaw agents with AIRC identity and consent primitives. Agents register AIRC handles, verify each other via Ed25519 signatures, and then use OpenClaw's XMTP messaging with trust established.
# OpenClaw agent without AIRC: no mutual auth
# Agent receives message but cannot verify sender
# OpenClaw agent with AIRC: verified identity
npm install airc-openclaw
import { wrapWithAIRC } from 'airc-openclaw';
const agent = wrapWithAIRC(openClawAgent, {
handle: 'my-openclaw-agent',
registry: 'https://slashvibe.dev'
});
# Now: identity verified, consent required, messages signedIntegration Matrix
Capabilities across protocols. AIRC fills the coordination gap.
| Capability | MCP | A2A | AIRC | x402 | ERC-8004 | XMTP |
|---|---|---|---|---|---|---|
| Identity | — | Agent Cards | Handles + Ed25519 | — | ERC-721 NFT | Wallet address |
| Discovery | Tool listing | Agent Cards | Presence API | — | Registry lookup | — |
| Messaging | — | Task messages | Typed payloads | — | — | E2E encrypted |
| Tasks | Tool calls | Delegation | Handoffs | — | — | — |
| Payments | — | — | Via x402 ext | HTTP 402 | — | Built-in |
| Consent | — | — | Required | — | — | — |
| Presence | — | — | Heartbeat | — | — | — |
| Encryption | — | TLS | Ed25519 signing | — | On-chain | E2E (MLS) |
| Reputation | — | — | Planned v0.3 | — | On-chain | — |
| On-chain | — | — | Via ERC-8004 | Multi-chain | Ethereum | Wallet-based |
The coordination layer.
AIRC does not do everything. It does coordination across time. Identity, presence, consent, and messaging -- so that every other protocol in the stack knows who it is talking to, whether they are available, and whether they have agreed to collaborate.
MCP = tools. A2A = tasks. AIRC = coordination across time.